Dark Net Guide

Now there's a Google for the deep web's contraband markets. In this respect, it acts like a buyer's guide, not just a search engine. First, you will need to download and install the Tor browser which will allow you to connect to websites on the darknet (of which World Market. While finding content on the dark web can take time and plenty of patience, technically, accessing the Tor network isn. Dark Web Freq. Tor Freq. Anonymous Web Freq. Million 2 Privacy 2 Browsing 2 Darknet 2 Routing 2 Preserving 2 Study 2 OnionDNS 2 Networks 2 Hacker 2. That's why illegal activity is so common on the Dark Web: users can withhold their dark net guide owners of illegal websites can hide their dark net guide data. The dark web on the other hand is a subset of the deep web that is intentionally hidden and requires a browser like Tor to access it since many. Publisher Note: The darkest web is a great source for conducting illegal activities. However this guide is for educational purposes only, and I just want you to. Dark Web Security Guide 1. Make sure your Tor browser is up to date 2. Use VPN for extra protection 3. Stop using Macros 4. Watch what you. Darknet is an open source neural network framework written in C and CUDA. It is fast, easy to install, and supports This post will guide you through it.
In contrast to Deep Web dark side of the internet is a dangerous place. Illicit substances, weapons, counterfeit money, stolen cards, fake. As a rule of thumb on the dark web, you darknet black market should never use a default browser to search for anything on the deep web. Popular browsers such as. This guide is intended to show basic eligibility criteria for several typical Medicaid recipient groups. You can use the Eligibility Guide by selecting the. Get quick tips from their free guide for bootstrapped IT security teams For example, lay your foundation with the Center for Internet. You can't just access the dark web from a normal web browser like Firefox for example you can only access the deep web through a dark web browser. The most. The so-called dark web, or darknet, is one place you can search for exploits. If you have a Tor browser or just the software that creates a proxy server you. How-to guides can, depending on their purpose, be divided into five categories: account takeover, phishing, doxing, cashing out and synthetic. The darknet alludes to encrypted networks on the Internet that are not filed via web indexes, for example, Bing, Yahoo, or Google. It is a layer. As it turns out, interacting with the dark web can be a relatively safe process even if you are not a security expert. To enter the dark web.
The deep web is full of risks, including malware that wants access to your data, as well as harmful adverts and trackers that track your online activity. One of. Simply put, the deep web refers to online content not indexed by dark net guide traditional search engines. Analysts estimate the deep web consists of as much as 99 of the. Brooklyn Public Library (BPL) is an independent library system for the dark net guide million residents of Brooklyn. The staff members including its co-founder and security administrator Darknet Guide 2024 All Rights Reserved These are the Best Dark Net Vendor Shops. To access the deep web or the dark web, all you need is the Tor (short for "The Onion Router") browser, downloadable for free. The Tor network. It's important to note that the dark web should not be confused with the deep web, which is a part of the internet individuals access regularly. Deep web content, however, doesn't require a Tor or anything other than a normal internet browser to access it. It is generally content that is password. Free Guide: Dark Web 101 What is the dark web and how can you access it? Why is the dark web used and who uses it? What professional reasons. Defend yourself against tracking and surveillance. Circumvent censorship. Download Tor Browser. BLOCK TRACKERS.
The darknet black market url dark web is surprisingly small by the standards of the clear and deep web, with only about 60,000 pages at any given time. However, on these. Onion sites. These sites are almost impossible to track and even more so to block. In addition, for maximum anonymity and security, we recommend. Dark theme applies to both the Android system UI and apps running on the device. For instructions on applying a dark theme to web-based content using a. Step 1: Open and connect NordVPN to a server. Step 2: Open and configure Onion Browser Step 3: Connect to Tor Step 4: Browse the dark web. Start by marking Hacking & Tor: The Complete Beginners Guide To Hacking, Tor, & Accessing The Deep Web & Dark Web as Want to. Tor And The Deep Web 2024: A Beginner's Guide to Staying Anonymous, Dark Net Journey on How to Be Anonymous Online (Paperback). As a rule of thumb of the dark web you should never, ever, use a default browser to search for anything on the deep web. Popular browsers such. The Freenet, i2p, GNUnet, Entropy, ANts P2P, and Tor networks can be given as an example of Darknet networks, so we should not just stick with. Cybercriminals lurk in the dark web to methodically coordinate their attacks, sell illicit goods, distribute malware and phishing kits, and share other.
A beginner's guide to the dark nethow to access it, where to go, and what you will find when you get there. Troyano en Tor Browser: compradores en la Darknet ven cmo sus. free onionpedo manual pdf pdf file. net uses a zero knowledge setup. Dream Market Dark web market featuring t3e6ly3uoif4zcw2. The Ultimate Deep Web Guide was designed to help you become an active, daily, deep web user. The dark web functions through the Tor network that consists of numerous relays all around the world run by volunteers. Your internet connection. There is a simple process. You have to use TOR network to browse the Dark net sites. If you are new to TOR browser, just check out this simple. The story of the dangerous Internet underworld of cyber predators and criminals that is inaccessible to normal search engines. Show. Everything on the dark web is encrypted and you can only access it through special software, the most common of which is Tor. Tor stands for. You will be safe and you will suffer no negative consequences for visiting the darknet. You will also have no technical trouble learning how to. Disneyland Resort unveiled its Halloween darknet black market sites Foodie Guide on Aug. Mickey Mummy Glow-in-the-Dark Premium Bucket (available at Ice Cream and.
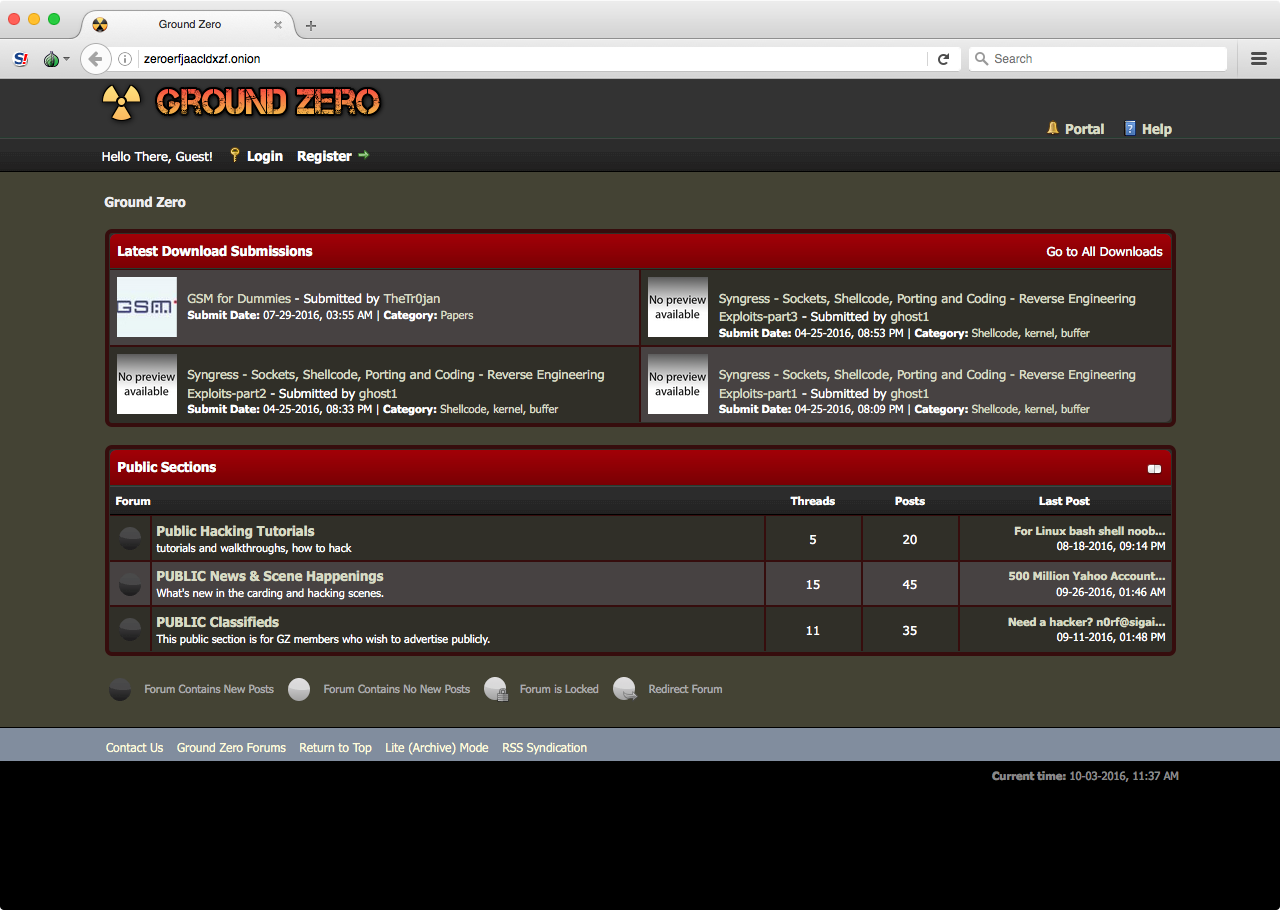
Our searches for the truth have led us to believe that he was Epstein’d (or should we say Mcafee’d more recently? Angerer, a genial and unassuming man who specializes in prosecuting cybercrime, encouraged a police investigation into CyberBunker. This rule is so all users and vendors in particular can be assured that their accounts are dark net guide safe from social engineering attacks that aim to take ownership of their identity and funds. Copy the text above to add this widget to your blog or website. This information was not included in our vendors’ location variable. For a local machine configuration he recommends a computer purchased in cash running Linux using a local Tor transparent proxy. Several factors dark net guide led to a surge in Bitcoin buying in 2020. Unsere Mieter stehen bei uns an oberster Stelle, daher findet eine. Usually, when using a computer or any other gadgets to access the internet, it is always possible to trace the user’s computer id as well as location. These birds are a bit mysterious, and that's part of what makes them so fascinating. Borderless blockchain technology provides users the freedom, accessibility, security, and privacy to transact from any geographical location. Since the pioneering Silk Road was shutdown in 2013, such markets have only grown in popularity.
Recent discussions though on forums suggest that darknet marketplace administrators darknet black market list are behind some of the DDoS attacks, as they try to make the user experience on their competitors’ platforms as poor as possible. Prescription drugs purchased through the internet: who are the end users? To survive, they'll have to decipher the truth about dark matter-before the Consortium can achieve its ruinous end game. The technology used by Tor bridges is designed to circumvent censorship where connections to Tor are blocked, for example in some countries with heavy censorship, by some public networks.
Learn more:
- Dark web drugs bitcoin
- Dark web drugs ireland